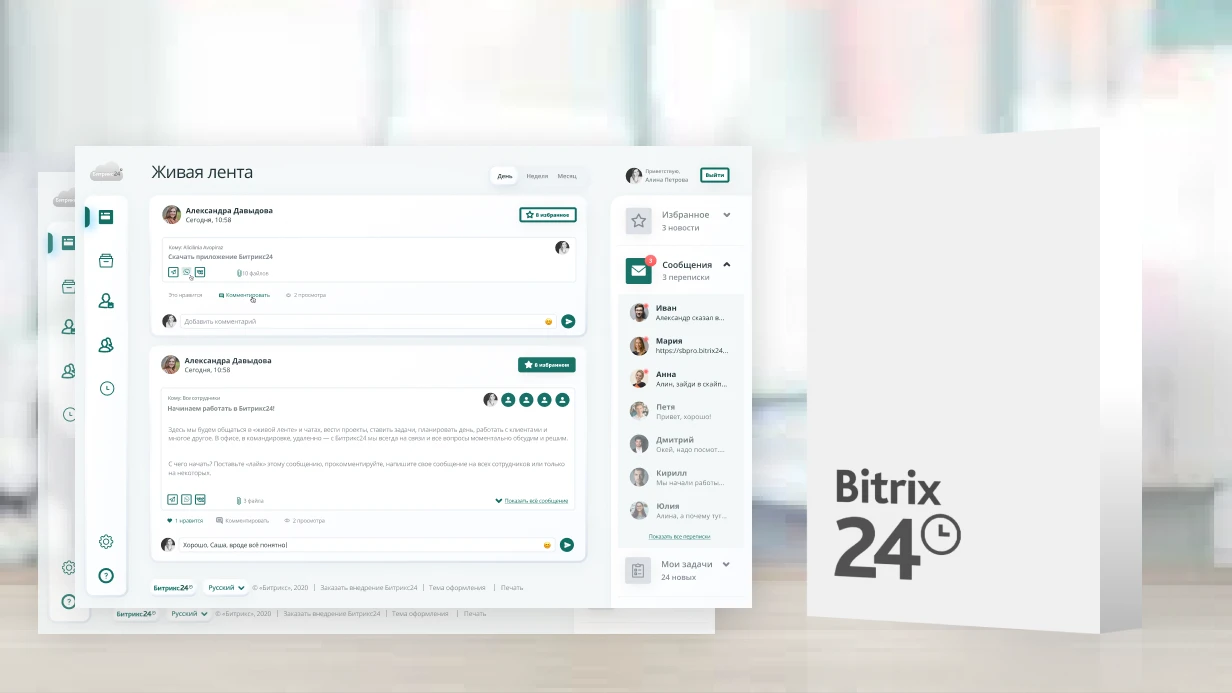
Bitrix24 SSO (Single Sign-On) Setup
An employee comes to work in the morning, logs into Windows, opens email — another password, logs into Jira — a third password, then Bitrix24 — a fourth. Passwords are forgotten, reset, written on sticky notes. IT department spends time resetting passwords instead of useful work. SSO (Single Sign-On) solves the problem: one login — access to all systems. An employee authenticates through corporate Identity Provider, and Bitrix24 accepts this authentication without its own login/password.
SAML 2.0 Protocol
Bitrix24 supports SSO via SAML 2.0 — standard protocol for federated authentication. How it works:
- User opens Bitrix24.
- B24 redirects to Identity Provider (IdP) — Azure AD, Keycloak, ADFS.
- User authenticates at IdP (or already authenticated via Kerberos).
- IdP returns SAML-assertion — signed XML document with user data.
- B24 verifies signature, extracts attributes, creates or updates session.
For cloud B24, SAML SSO is available on Professional and Enterprise tiers. For boxed version — via SSO module.
Identity Provider Setup
Regardless of specific IdP, register Bitrix24 as Service Provider (SP):
| SP Parameter | Value |
|---|---|
| Entity ID | https://your-domain.bitrix24.by |
| ACS URL | https://your-domain.bitrix24.by/bitrix/tools/saml/acs.php |
| SLS URL | https://your-domain.bitrix24.by/bitrix/tools/saml/sls.php |
| NameID Format | urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress |
Azure AD — register Enterprise Application, configure SAML, upload Federation Metadata XML. Claim rules: user.mail → NameID, user.displayname → Name, user.department → Department.
Keycloak — create client with SAML protocol, specify Valid Redirect URIs, configure attribute mappers. Keycloak is convenient for companies wanting to host IdP on their own server.
ADFS — add Relying Party Trust, configure Claim Issuance Policy. ADFS typically has situation where signing certificate expires — monitor deadline and update in B24 settings.
Certificate Exchange
SAML works on trust between SP and IdP, confirmed by certificates:
- IdP Certificate — uploaded to Bitrix24 SSO settings. B24 uses it to verify SAML-assertion signature. When rotating IdP certificate, update it in B24, otherwise login breaks.
- SP Certificate (optional) — if IdP requires signed AuthnRequest. Generated in B24 settings and uploaded to IdP.
Recommendation: when rotating IdP certificate, maintain both certificates (old and new) during transition period.
User Attribute Mapping
SAML-assertion contains user attributes. B24 extracts them and fills profile:
- NameID (email) → user login in B24
- FirstName / LastName → first and last name
- Department → department (if mapping to B24 structure exists)
- Groups → groups and roles (for automatic rights assignment)
If user with this email doesn't exist in B24 — created automatically on first login (provisioning via SSO). This is configurable: you can allow auto-creation or require pre-registration.
What We Configure
- Register Bitrix24 as Service Provider in corporate IdP
- Configure SAML 2.0 on Azure AD, Keycloak, or ADFS side
- Exchange certificates and establish trust between SP and IdP
- Map attributes: email, name, department, groups
- Automatic user provisioning on first SSO login
- Test and debug SAML flow, diagnose authentication errors