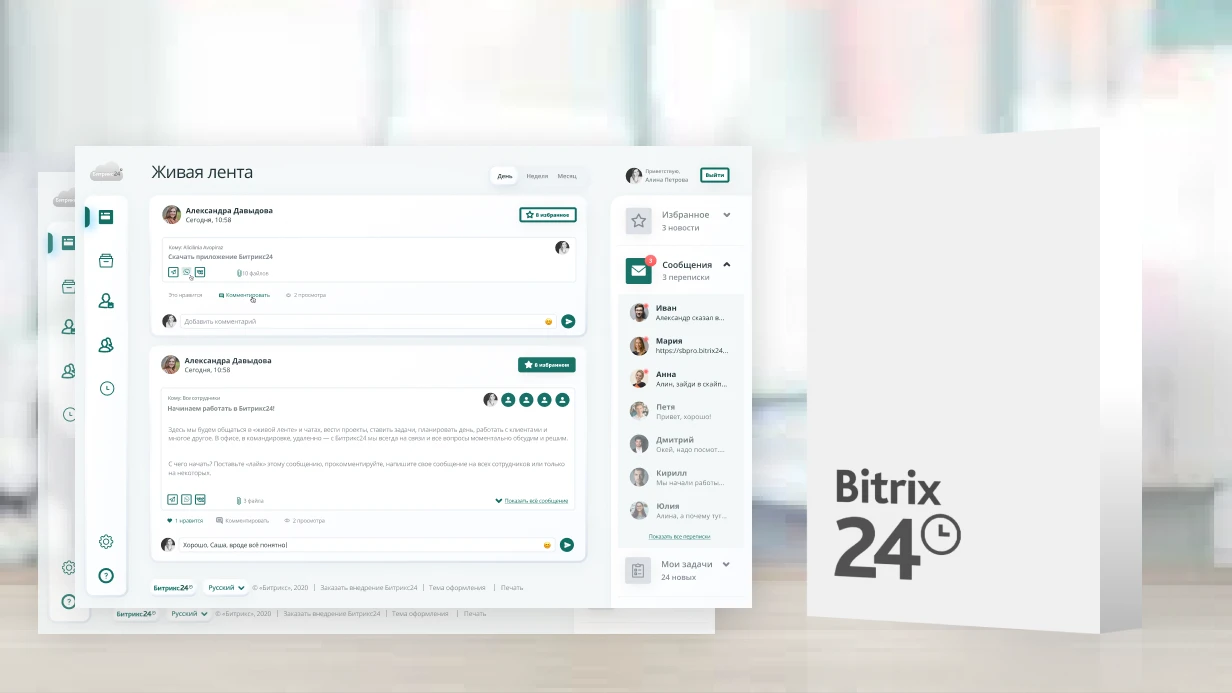
Proactive Protection Setup in 1C-Bitrix
Proactive protection in Bitrix is the built-in security module that analyzes incoming requests and blocks XSS, SQL injection, CSRF, and a range of other application-layer attacks. When misconfigured, it either fails to protect or blocks legitimate requests.
Security Module Components
The security module includes several subsystems, each configured separately under Settings → Proactive Protection:
- Proactive filter — analyzes GET/POST parameters against attack patterns
- Web Antivirus (WAF) — advanced filtering with signature-based analysis
- Activity control — detects abnormally frequent requests from a single IP
- Stop list — manual and automatic IP blocking
-
Intrusion log — the
b_security_logtable in the database
Configuring the Proactive Filter
Security → Proactive Protection → Proactive Filter:
Operating mode:
-
Disabled— logging only, no blocking (use during initial setup) -
Active— blocks suspicious requests with a redirect to an error page -
Paranoid— additional checks; false positives are possible
Recommended approach: first enable logging mode for 3–7 days, review the logs, whitelist legitimate requests, then switch to active mode.
Exceptions: paths like /bitrix/admin/, API endpoints, and file upload paths frequently trigger false positives. Add exceptions for specific URIs rather than wildcard masks.
Activity Control and Stop List
Security → Activity Control — configure thresholds:
- Maximum number of requests from a single IP per time period
- Action on threshold exceeded: redirect, CAPTCHA, or block
Blocked IPs are stored in b_security_stop_list. Configure automatic unblocking via the agent \Bitrix\Security\Stoplist::clearOldRecords().
Real-World Case
An online store was hit with an attack targeting the search form: SQL fragments (' OR 1=1 --) were being passed in the q parameter. The built-in Bitrix filter did not respond — it had been enabled in logging mode and never switched to active. The b_security_log table contained 800+ entries in a single day. After switching to active mode and adding the attacker's IP to the stop list, the attack stopped.
Logging and Monitoring
Regularly review b_security_log — entries with SEVERITY = 'CRITICAL' require immediate investigation. Set up email notifications via the SECURITY_CRITICAL_EVENT mail event (created manually under Settings → Mail Events).
Delivery Time
Proactive protection setup with log analysis and exception configuration — 4–8 hours depending on project complexity.